The Fitsec Cyber Threat Intelligence feed is a collection of data used to identify malware fingerprints and attacks targeted towards an organization. It is designed to be easily integrated into your existing systems and to improve your malware detection capabilities. With Fitsec Feed, your organization is equipped to possibly stop an advanced attack altogether, or at least minimize the damages to your operation.
•••
What is an APT?
Targeted attacks are often referred to as APTs (Advanced Persistent Threats). The target is usually carefully selected and specific, and it can be a company or an individual office. By using multiple phases to break into a network and limiting the target range, targeted attacks become increasingly difficult to detect.
The attackers usually hold key information about the target organization, which they use to gain access to the network by using multiple technical and social methods. APTs are commonly long lasting and invisible to the target organization itself. Usually the main goal of an APT is to capture critical information and/or obstruct the operations of an organization by attacking their infrastructure.

APT-FEED
Protect your organization from advanced threats with the latest indicators on malicious activity. The Fitsec APT-feed provides you with data of the latest IOCs (Indicators of Compromise), which is data that is designed to be integrated into various systems in your organizations' network infrastructure. These systems can include firewalls, IDS/IPS systems, SIEM systems etc. IOCs enable you to monitor your network environment for signs of infection or abnormal behavior before damages are inflicted. The APT-feed is available in the following formats by default. We can also deliver the feed in any other format you require. We will also help with the integration if needed.
OUR COMPETITIVE ADVANTAGES:
WHY CHOOSE US?
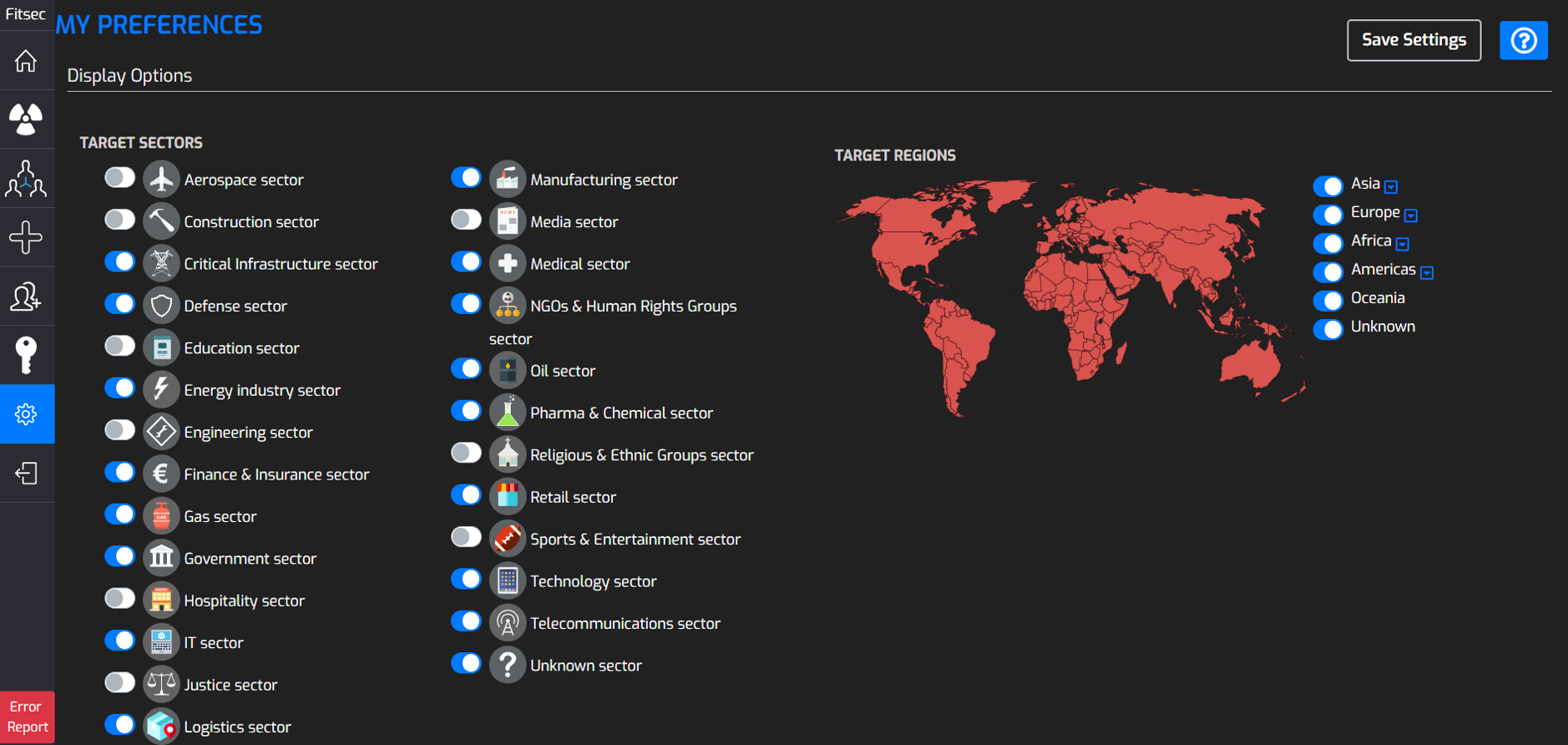
APT PLATFORM
The APT-platform, available as an additional service, is a valuable tool for SOC teams and threat hunting teams to help with day to day operations. For SOC teams, the tool can assist with data enrichment and scoring threats and for threat hunting teams our platform can act as a library of historical and current data about APT actors to improve defences and make better decisions.
With this insight, teams can make better suggestions to executives. The clear grouping of threats and visual representation can help upper management better understand the threat landscape.
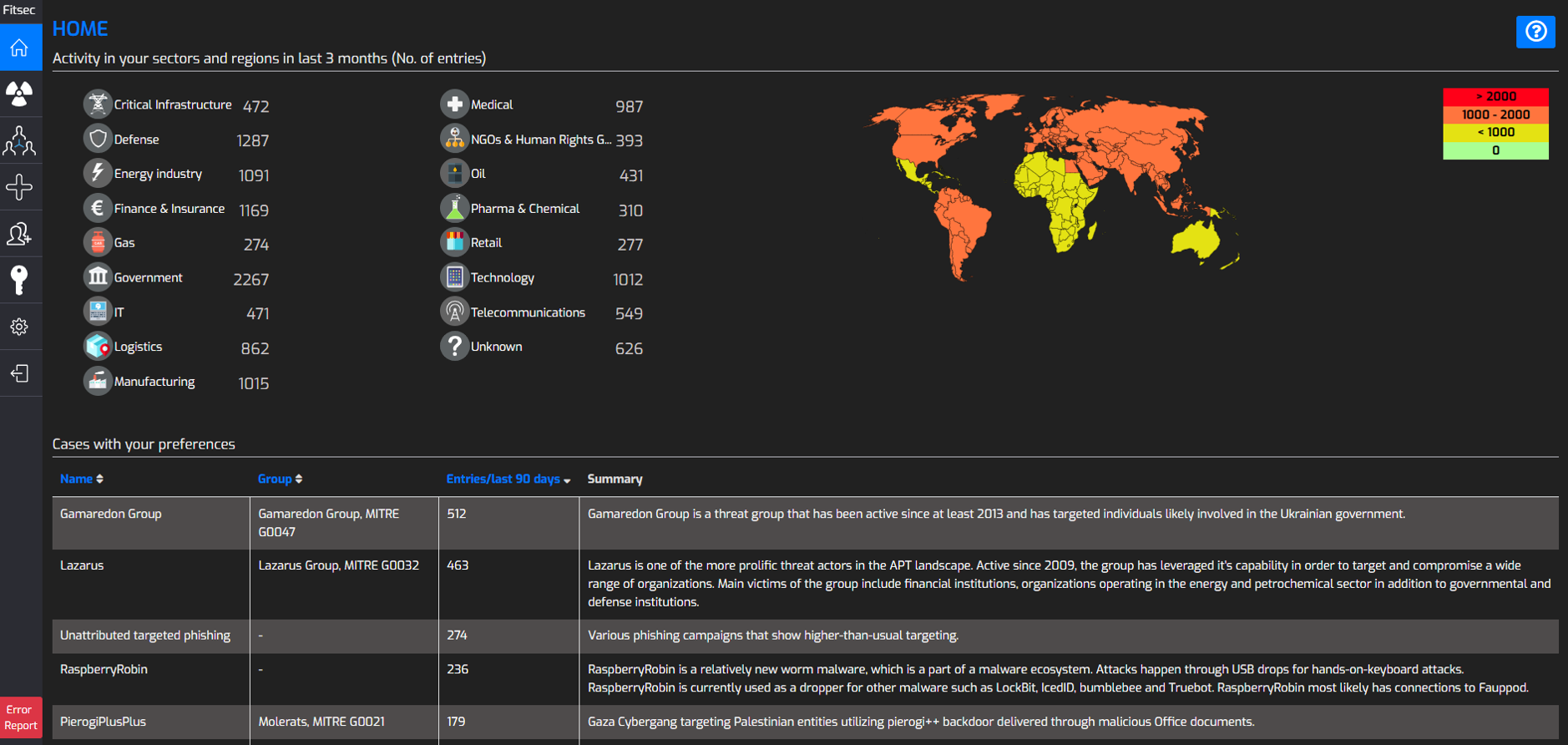
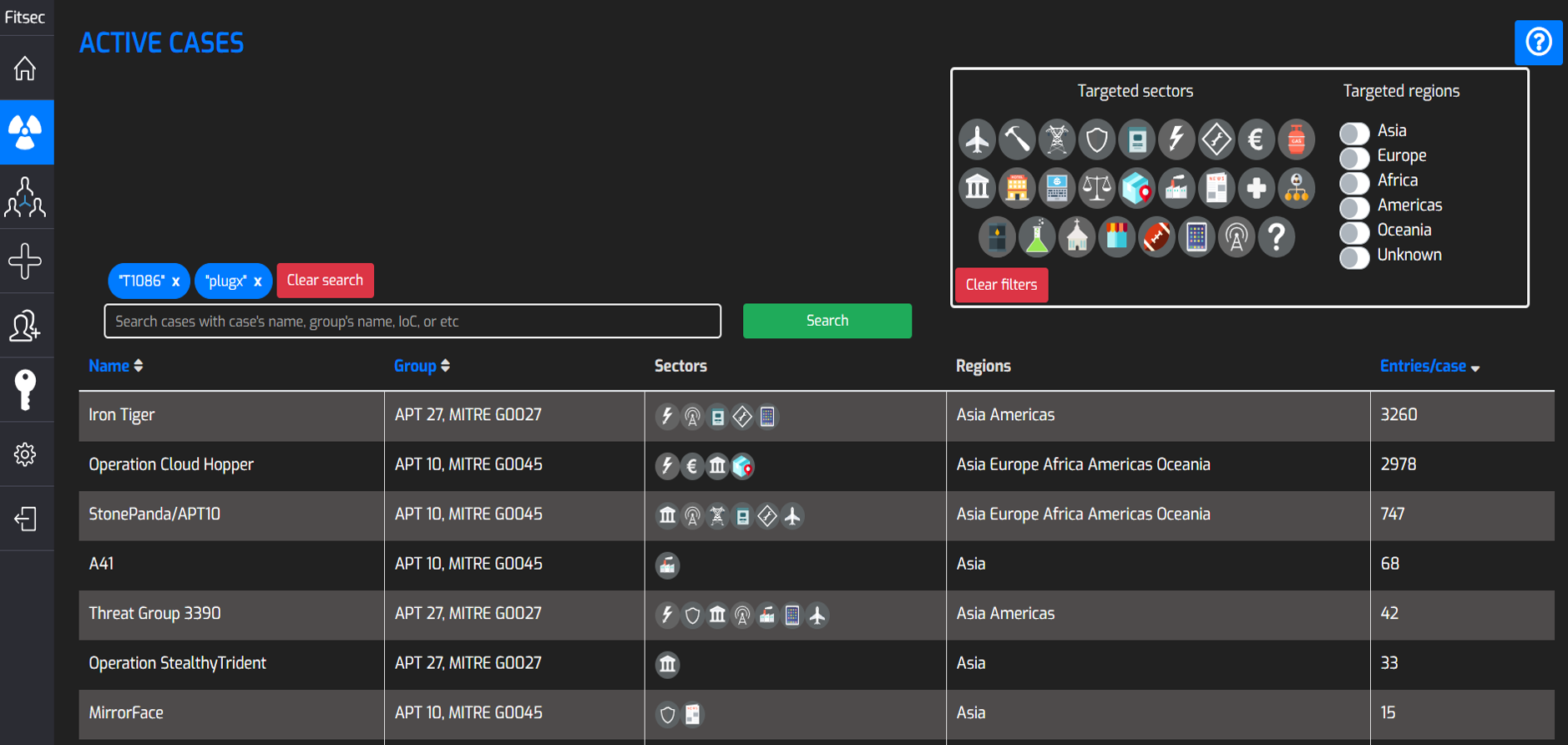
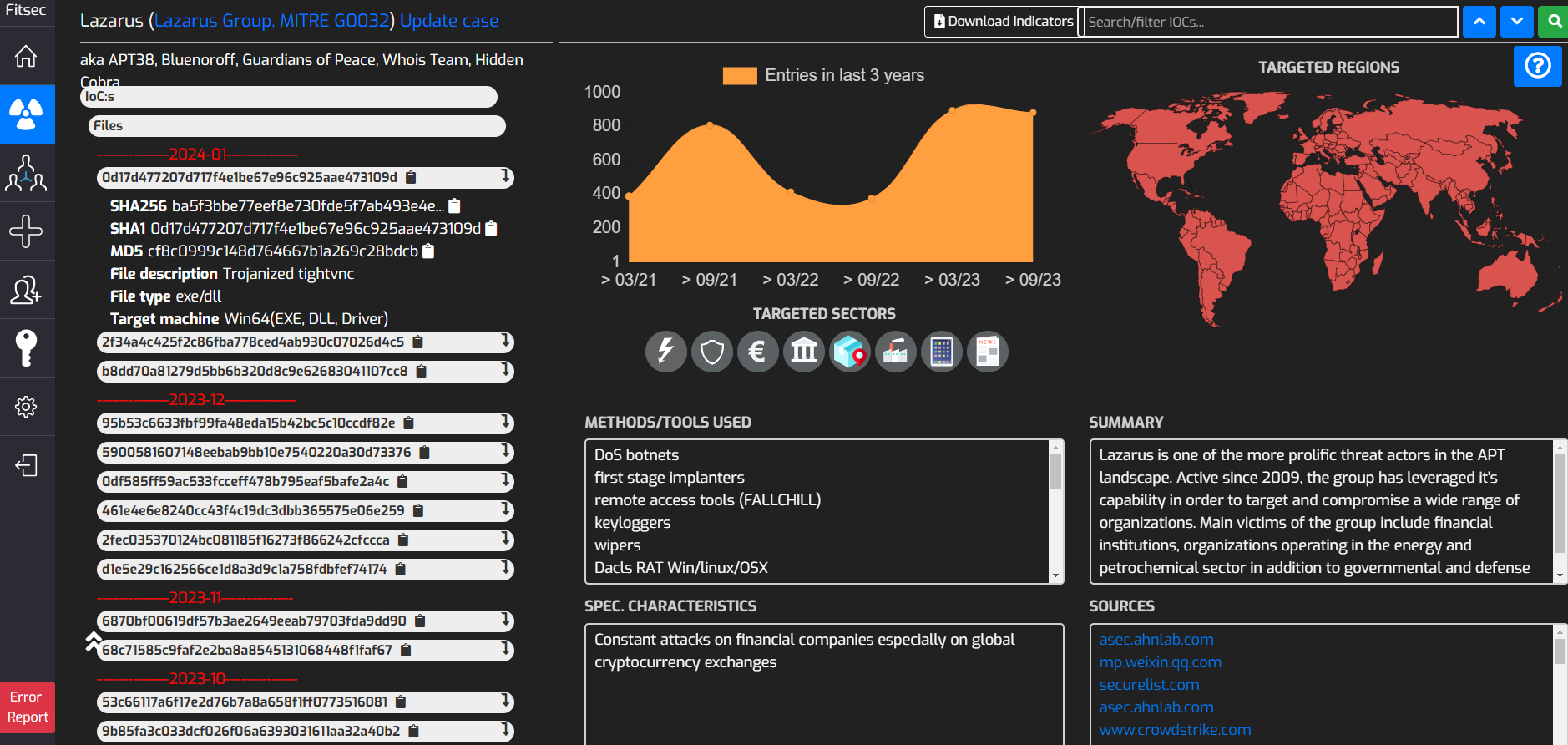
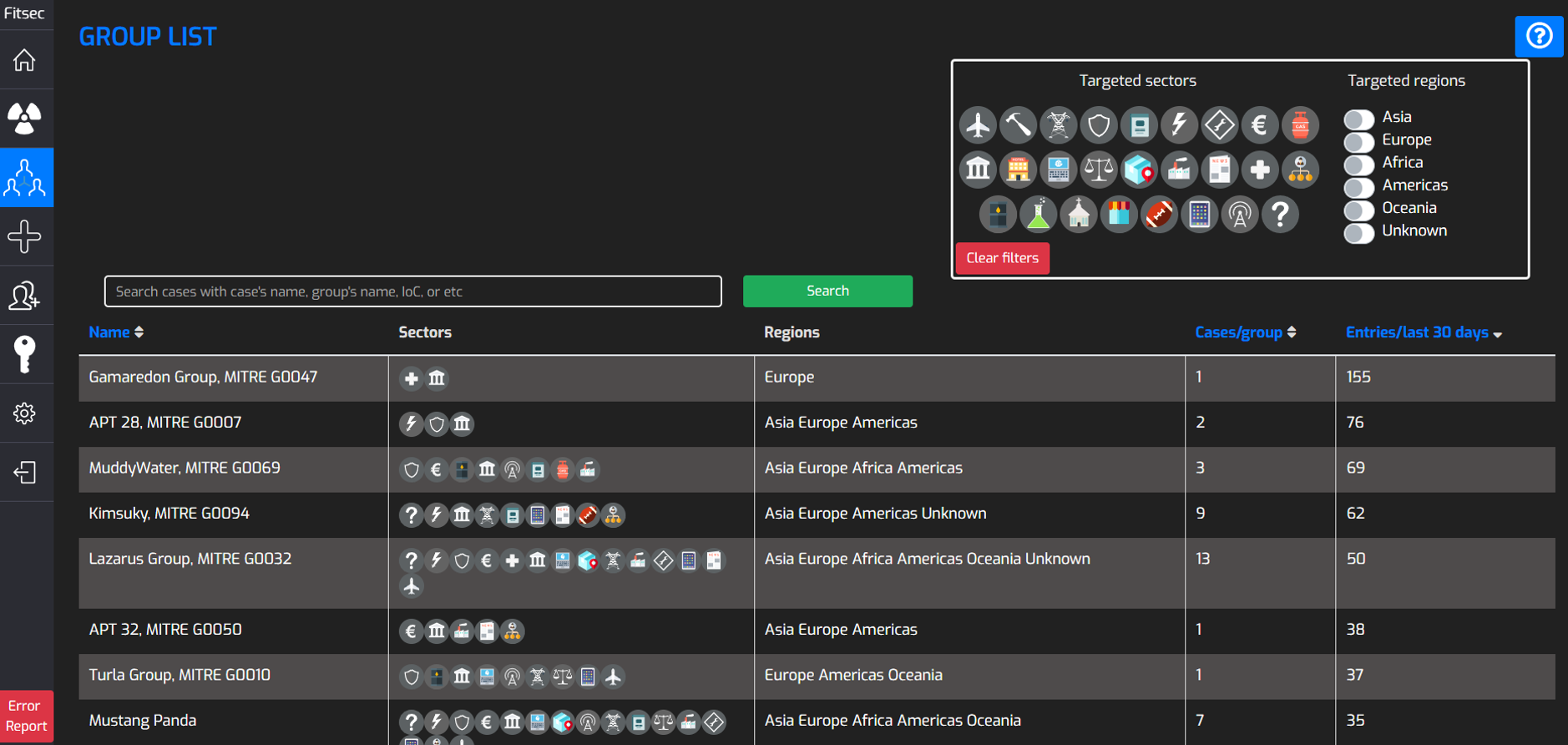
The platform is a web application that enables you to view and search all data related to threat actors in our database and visualize the amount of APT activity in certain sectors and countries. Below are some screenshots of the user interface and it's functionalities.
TESTIMONIAL
"The Fitsec feed has a broad array of high quality technical IoC's that allow us to integrate it to the whole cyber kill chain. From network devices to workstations and servers, we are able to protect our primary assets on several different levels."
DEFENCE
CAN WE PROTECT AGAINST TARGETED ATTACKS?
Completely protecting against APTs is not possible; however with quick detection and response times you can minimize the damage done to your organization.
To aid quick detection and response times, it is a good idea to educate your staff and raise awareness on how to detect APTs and how to act in the event of an attack.
Other best practices for protection include keeping your software up to date, installing antivirus and anti-malware products on all your systems, monitoring your networks and utilizing cyber threat intelligence feeds to detect malicious activity in your networks.
It is also best to avoid opening unknown links to websites and to avoid connecting unknown USB-storage devices to your systems, as these can make you vulnerable to attacks.
HAS OUR NETWORK BEEN BREACHED?
Suspicious activity includes logins to new or unusual systems or logins during unusual times. Increased network activity during or outside office hours can also be an indicator of a breach. Other indicators of a breach can include system slowdowns, unusual software updates or connection problems.
Also, indicators of an ongoing attack or upcoming breach to gain sensitive information can include unusual calls or emails to your staff.
If you have any reason to believe your network has been attacked or breached, it is best to consult a professional as soon as possible to prevent further damage.

WHY CHOOSE FITSEC?
Our service differs from similar solutions because we manually segment and filter the data from the reports and scanners. We also emphasize the contents of our feeds based on the individual customer and their threat landscape. In the case of targeted attacks, we focus our malware analysis on APT-actors that have previously targeted the industry segments of our customers.

IS THE FITSEC FEED RIGHT FOR US?
Any organization monitoring the information security status of their networks will benefit from the intelligence gathered by our APT-feed. Also, all organizations that handle sensitive data should be actively looking for ways to mitigate the damages caused by targeted attacks. Our APT-feed can be a crucial tool for organizations in these segments: Governmental institutions, critical infrastructure, network operators, etc.
Detect Anomalous Traffic / Behavior: Monitor network activity and identify suspicious behavior signaling potential cyber attacks
Trend and Pattern Recognition: Analyze long-term data to identify trends in threat evolution and recurring patterns
OUR OTHER FEEDS
DDOS-FEED
The Fitsec DDOS feed offers intelligence on the latest DDOS threats and it reports on threats that are targeted against an organization's network infrastructure. The data provided by the DDOS feed includes malicious C2 (command and control) commands issued and the origin of the attack in real time.
The DDOS feed is especially beneficial to operators or other organizations that have critical online services and want to monitor the information security status of their networks.
SANDBOXIOC-FEED
The Fitsec SandboxIOC feed contains network IOC data that gives detailed insight into malware C2 (command and control) servers, enabling your security team to do prioritized response against internal malware infections to prevent further damages from occurring.
The SandboxIOC feed is crucial to network operators, governmental institutions and other organizations who need to detect malicious behavior in the network perimeter before malicious activies damage their business.
SINKHOLEIOC-FEED
The Fitsec SinkholeIOC feed listens to the traffic and detects the stolen data. As a client you will get BOT data such as infected IP addresses and information on the malware that has been detected. The Sinkhole feed provides actionable intelligence on hundreds of thousands of infected, malicious systems globally.
The SinkholeIOC feed is especially beneficial to operators and Governmental Institutions, and for anyone else who has the need to locate malicious systems.
Looking to Safeguard Your company’s private network?
CONTACT US TO BEGIN